eSecurity Planet may receive a commission from vendor links. Our recommendations are independent of any commissions, and we only recommend solutions we have personally used or researched and meet our standards for inclusion.
Network access control (NAC) solutions are a critical network security component, enabling IT security teams to verify the authorization and access levels for every device and user connecting to the network and quarantine devices that fail to meet security requirements.
Here are nine top NAC solutions, with an analysis of their strengths and key features of each, followed an assessment of the NAC market and the most important features to consider during tool evaluation.
- Aruba ClearPass – Best Large-Scale Guest Solution
- Cisco Identity Services Engine (ISE) – Best for Enterprise Deployments
- Extreme Networks ExtremeControl – Best to Balance Security and Operations
- Forescout Platform – Best NAC for Diverse Networking Environments
- Fortinet FortiNAC – Best for IoT and OT Needs
- InfoExpress CyberGatekeeper – Best for Rapid, Self-Controlled NAC Deployment
- Ivanti Policy Secure – Top Enterprise Alternative
- Opswat MetaAccess – Best for Smaller Security Teams
- Portnox Cloud – Best Option for SMBs
- What is Network Access Control (NAC)?
- How the Top NAC Solutions Were Selected
- Bottom Line: Control Network Access ASAP
1 Twingate
Twingate helps companies to easily implement a secure Zero Trust Network Access solution without compromising on usability or performance. Twingate replaces legacy VPNs with a modern Identity-First Networking solution that combines enterprise-grade security with a consumer-grade user experience. With the ability to support many thousands of users working from any number of locations, Twingate also works with all major cloud and identity providers and can be set up in less than 15 minutes.

Aruba ClearPass
Best large-scale guest solution
Aruba, a Hewlett Packard Enterprise company, deploys the ClearPass family of solutions for network access control within the organization’s network. The ClearPass family includes ClearPass Policy Manager, which enables security teams to define business-level access policies; ClearPass OnGuard for agentless endpoint security assessment; and ClearPass OnBoard, which streamlines bring your own device (BYOD) connectivity.
The ability to cluster both virtual and physical devices allows Aruba ClearPass to scale enormously. Combined with automated onboarding and Guest role options, Aruba ClearPass is suitable for use in stadiums, public festival space, and other high-volume guest-access needs.

Pricing
HPE Aruba offers three types of mutually excludable licenses: permanent, subscription, and evaluation. Each appliance must have a Policy Manager Platform base-level license (available as permanent or evaluation only). ClearPass application licenses are also sold based on the level of capabilities required:
- Entry licenses: Available as permanent or evaluation licenses that support a limited number of core features
- Access licenses: Enable the full suite of features, authentication types, and Guest functionality and are available as permanent, subscription, or evaluation licenses
- Access Upgrade licenses: allow the upgrade of an Entry license to an Access license and area available as a permanent license only
- OnGuard licenses: A permanent, non-expiring license for Policy Manager OnGuard
- Compliance Suite licenses: Available in one, three, and five year subscriptions and enable Policy Manager to integrate with Device Insight
- Onboard licenses: sold with a minimum of 100 licenses and available as permanent, subscription, or evaluation to allow Onboard-generated device certificates
Costs vary based upon the appliance, level of support, the number of devices supported, and duration of the licenses. HPE Aruba provides an ordering guide and will list prices on their website, but those sales will be fulfilled by partners. Prices through partners may be eligible for promotional or bulk discounts. Estimated prices are:
- Appliances range between $7,500 (500 concurrent sessions) and $20,300 (25,000 concurrent sessions) for physical appliances and VM versions cost $4,300
- ClearPass Access for 100 concurrent endpoints costs between $1,670 for a one year subscription and $2,800 for a perpetual license
- ClearPass Entry for 100 concurrent endpoints costs $710 (perpetual license)
OnBoard, OnGuard, and other add-on options require separate licenses.
Features
- Multiple enforcement methods (RADIUS, TACACS, SNMP) supported as well as OnConnect proprietary non-RADIUS enforcement
- User database options for Active Directory, LDAP, and SQL
- Device fingerprinting and comprehensive posture assessment identifies type and model name, MAC address, IP address, network interface card vendor, operating system and version
- Onboarding options for defining authority to onboard corporate and bring-your-own-device (BYOD) devices and number of onboarded devices per user
- Context-based policy engine supports granular policy enforcement using user role, device type, authentication method, location, time-of-day, and more
- Robust Guest access options are customizable for branding or sponsor-based approvals to allow self-service, temporary guest accounts to access the network
Pros
- Vendor agnostic: can propagate access policies for other vendors, including Cisco
- Integrates security alerts from over 170 security and IT management solutions and can act as a clearing house for attack alerts
- Flexible deployment options: Physical or virtual appliances; stand-alone or deployed in clusters
- Single-sign On (SSO) support for Ping, Okta, and more
- IOT device support using MAC address authentication
Cons
- Requires multiple licenses to establish functional NAC
- Little community support for self-help or advice
- Complex and challenging setup and integration
For the full list of features, pros, cons, and more details on pricing, see our in-depth Aruba ClearPass Policy Manager Review.

Also read: Network Protection: How to Secure a Network
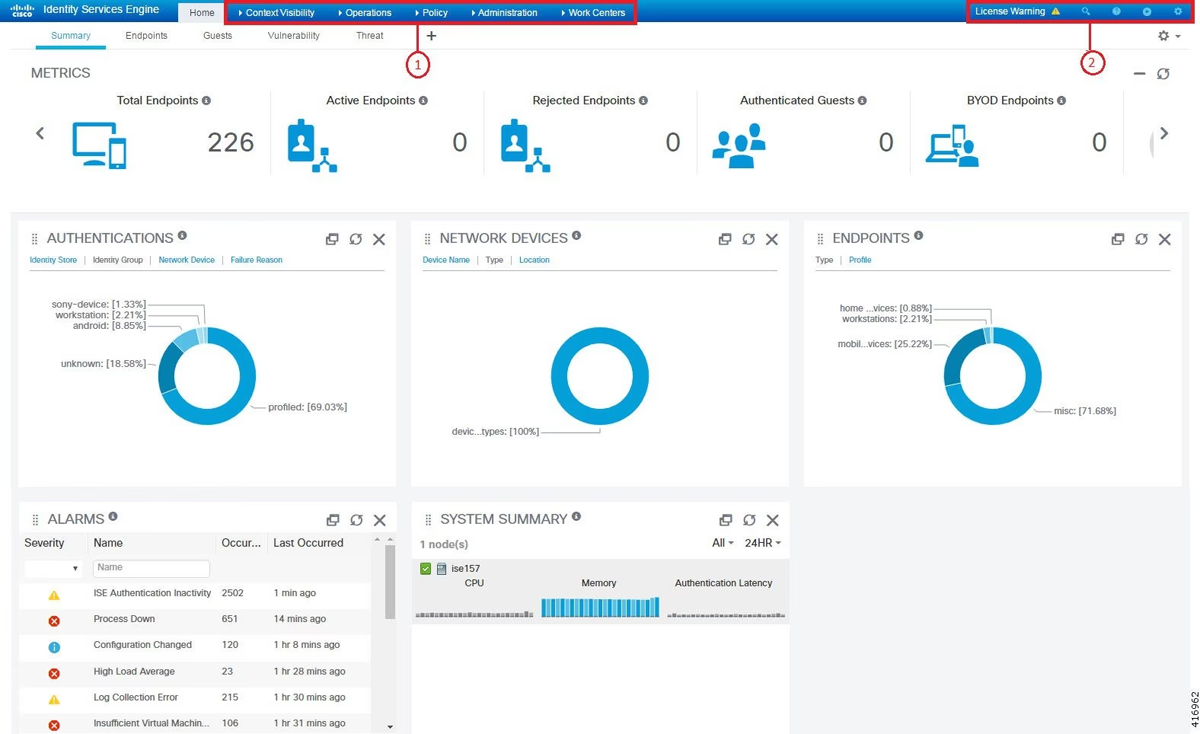
Cisco Identity Services Engine (ISE)
Best for enterprise deployments
As the dominant brand in networking, Cisco’s Identity Services Engine (ISE) may be the best option for many enterprises because it can immediately plug into existing Cisco networking ecosystems. ISE also provides modules for managing network devices or to integrate with security tools to provide robust security. ISE is intended for use with guest and employee endpoints, and Cisco also offers separate and specialized NAC solutions for equipment (internet of things (IoT), operational technology (OT), and industrial controls), for medical devices, and for rapid threat containment.
Pricing
The ISE Base License is perpetual; however, the Plus, Apex, Mobility, and Mobility Upgrade components may only be licensed on 1, 3, or 5 year subscriptions. Cisco also offers Smart Licensing through a centralized Cisco Smart Software Manager (CSSM) database and negotiated enterprise agreements.
Deployment of ISE requires an appliance plus software licenses plus service contracts (for technical or advisory services). Cisco offers virtual appliances, cloud-native ISE, and specially configured Cisco Secure Network Servers configured for physical ISE appliance deployment. Cisco Capital also can provide flexible payment options to ensure predictable payments.
Cisco’s secure network servers come in three basic sizes:
- Small (starting above $13,000); supports 12,500 to 25,000 users
- Medium (starting above $30,000) supports 25,000 to 50,000 users
- Large (starting above $58,000), supports 50,000 to 100,000 users
- Virtual machine (VM) licenses are estimated to be under $2,000 for electronic delivery of a single license, but expect bundles to be available for multiple licenses
Cisco offers several different ISE software licenses:
- ISE Essentials required for: Guest accounts, secure wireless access, and basic asset visibility
- ISE Advantage required for SGT or SGACL secure wireless access, advanced asset visibility, automated BYOD onboarding, rapid threat containment, network segmentation, and security ecosystem integration
- ISE Premier required for device compliance analysis
- ISE Virtual Machine (VM) licenses are required for each virtual machine deployment and estimated to be under $2,000 for electronic delivery of a single license.
- Device Admin license required for the administration of network devices (licensed per policy service node (PSN)
- Cisco DNA Center: Required for Cisco advanced asset visibility
Additional licenses may be required to connect with other Cisco products (AnyConnect, AnyConnect Stealth, pxGrid, etc.). Cisco ISE offers cloud-native options that can be licensed directly through Cisco resale channels or purchased through Amazon Web Services (AWS), Microsoft’s Azure marketplace, or Oracle Cloud Infrastructure (OCI).
Features
- Strong guest account options:
- Hotspot: non credentialed access
- Self-Registration: guest enters info, can require approval
- Sponsored Guest: authorized creation of account and share credentials
- Secure wireless connection options:
- Passive Identity session (using Active Directory (AD) domain logins, etc.)
- Assign user to a virtual local area network (VLAN)
- Discretionary access control list (DACL)
- Downloadable agents: layer 2 port Access Control (ACL), Security Group Tags (SGT), or Security Group Access Control List (SGACL).
- Asset visibility options:
- Basic: match endpoint network attributes to known profiles to categorize endpoints and enforce policies based on asset profile
- Advanced: Artificial Intelligence (AI) enhanced Deep Packet Inspection (DPI) of network traffic between the device and other network assets
- Device compliance analysis:
- Deploy a persistent or temporal agent to analyze the device for compliance with patching, antivirus, etc.
- Variable access can be applied based on level of compliance
- Can use ISE Posture Engine or integrate with existing Mobile Device Management (MDM) or Enterprise Mobility Management (EMM)
- Automated BYOD onboarding: enables bring-your-own-device (BYOD) connections to be automated using built-in certificate authority (CA), BYOD registration, and integration with MDM or EMM
- Rapid threat containment:
- Changes account privileges in the event of suspicious activity, detected vulnerabilities, or known threats
- Automatically or manually moves devices to sandboxes, remediation domain, or denies complete access
- Network segmentation controller simplifies the management of switch, router, wireless and firewall rules to reduce costs and the time to implement changes significantly over traditional segmentation
- Security ecosystem integration with compatible next generation firewalls (NGFWs), threat feeds, and other third party systems permits two-way enhancement of the security stack
- Device administration enables the onboard of network devices (routers, switches, firewalls) and remote administration of configurations through ISE
- Government certified FIPS 140-2, Common Criteria type, Unified Capabilities approved list
Pros
- Consolidated and centralized network control in a single solution for both users and networking devices
- Enables zero trust principles with software defined networks, segmentation, and granular access control
- Reduced IT workload through self-service on-boarding
Cons
- Confusing and expensive licensing
- Non-intuitive and complex user interfaces
- Poor 3rd-party integration with non-Cisco products
For the full list of features, pros, cons, and more details on pricing, see our in-depth Cisco Identity Services Engine (ISE): NAC Product Review.

Extreme Networks ExtremeControl
Best for balancing security and operations
Extreme Networks’ ExtremeControl network access control offering delivers a single pane of glass solution with context-based network control for both wired and wireless networks. Optional licenses enable simple device onboarding for IoT (Internet of Things) and guests, as well as security posture assessment.
As a leader in networking, Extreme Networks deeply understands networking requirements for complex environments that include a mix of cloud and on-premises operations. The ExtremeControl NAC creates both security and operations alerts to provide a balanced solution for secure and smoothly-running networks.
Pricing
Extreme Networks does not publish pricing directly, but published reseller pricing enables rough estimates that do not reflect potential partner programs, bulk pricing, or other incentives. Extreme Networks professional services, product service, and support will require additional fees. Virtual deployment appears to require additional software and licenses.
- Physical appliance
- $15,300 for 12,000 endpoints IA-A-25
- $24,800 for 24,000 endpoints IA-A-305
- Perpetual NAC licenses
- $8,000 for 1k end systems IA-ES-1K
- $22,500 for 3k end systems IA-ES-3K
- $85,000 for 12k end systems IA-ES-12K
- Optional Perpetual Posture Assessment licenses
- $12,000 for 3k end systems IA-PA-3K
- $48,000 for 12k end systems IA-PA-12K
- Optional Guest and IoT Onboarding license
- $3,000 for 1k end systems IA-GIM-1K
- $6,000 for 3k end systems IA-GIM-31K
- $12,000 for 12k end systems IA-GIM-12K
- Subscription license (97207-27001)
- Includes an unlimited number of end-system licenses up to the performance limit plus Extreme works
- Priced at $12 per user per year
- Requires appliance ownership
Features
- Third party integration with many third-party security tools such as firewalls, security information and event management (SIEM) tools, mobile device management (MDM), and enterprise mobility management (EMM) solutions
- Guest and IoT onboarding (additional license required) manages expiration, account validity and time control without requiring IT oversight or approval
- Device profiling of type, security posture, etc.
Pros
- Wired and wireless network access control
- Context-based policies that consider security posture of endpoints
- Detailed profiling with access and app analytics data
- Per user pricing available
Cons
- Product feature gap: more robust features may be found in the cloud-based solution than the on-premises appliances
- Poor information on virtual appliance licensing and capabilities
For the full list of features, pros, cons, and more details on pricing, see our in-depth Extreme Networks ExtremeControl: Network Access Control (NAC) Product Review.
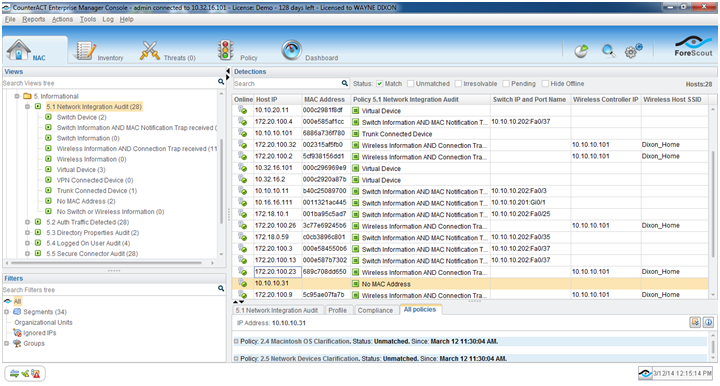
Forescout Platform
Best NAC for diverse networking environments
Forescout Platform’s vendor agnostic and non-disruptive installation enables integration with network devices from a wide variety of vendors (Cisco, Juniper, etc.) and quick deployment for modern, sprawling and varied network environments. Forescout Platform requires no changes to network designs and their long NAC experience and prominence means a huge number of established 3rd-party integrations.
Forescout’s Platform began as the CounterACT network access control (NAC) solution and now contains nearly a dozen modules. The various add-on licenses deliver real-time asset inventories of all IP-connected devices, policy based network access controls, security integration, and much more.
Over 20 active and passive discovery and profiling methods replace agents in profiling devices based upon their activity, MAC addresses, and other factors. Forescout Platform detects more than 12 million devices to extend NAC controls to the cloud as well as to varied industrial and medical industries.
Pricing
Forescout does not publish pricing information directly, but does publish a licensing sizing guide that covers hardware options and some software licensing requirements. Partner pricing can be located, but may not reflect promotions, bulk discounts, or bundled pricing opportunities.
Forescout Platform deploys on physical or virtual appliances. For small deployments, the Forescout license can be installed directly on the appliance, but for larger deployments one appliance will need to be dedicated as an eyeManage appliance to manage other Forescout appliances.
Virtual appliance licenses include the Forescout virtual appliance, Forescout eyeManage, and the Console. Virtual Appliances are licensed based on the number of devices managed in five sizes from extra small (up to 100 licenses) to extra large (up to 20,000 licenses).
In addition to appliances, the Forescout Platform modules are offered in perpetual, term-based licenses of one or three years, or subscriptions. Perpetual and term licenses are available for eyeSight, eyeControl, and eyeRecover. Sufficient eyeSight licenses are required to license eyeControl, eyeExtend, eyeSegment, and other add-on modules.
Licenses are based on the number of devices controlled where devices are counted by IP or MAC address. Flexx Licensing enables flexible software-centric licensing to streamline license management, and enable easy deployment of additional licenses on-demand.
Features
The Forescout Platform NAC tools each provide specific features:
- eyeControl Features
- Granular enforcement access based on device classification, security posture, and user (employee, guest, contractor, etc.) combinations
- Enables automated response to quickly and effectively contain threats based upon policy from moderate (move to guest network, assign to self-remediation VLAN, apply OS updates/patches, etc.) to stringent (quarantine assets, turn off switch port, block access, disable network card, etc.)
- Automated onboarding of new devices, including bring-your-own-device (BYOD) endpoints and guest users
- eyeSegment Features
- Simulate updated policies to determine how they will impact operations prior to activation
- Enable Zero Trust initiatives with zones, groups, and micro-segmentation of the network based upon users, devices, and applications
- Real time monitoring of network segments to enable automated or rapid response to policy violations or security threats
- eyeSight Features
- Continuous monitoring and detection of devices in the enterprise as they connect to the network
- Realtime asset inventories of physical and virtual devices, including auto-classification for a wide variety of Internet of Things (IoT), Internet of Medical Technology (IoMT), Operations Technology (OT), cloud technologies, and industrial devices (IIoT)
- Passive profiling and assessments of devices provides deep insight without impacting performance or uptime
- Medical Device Security Features
- Continuous detection of medical devices
- Artificial Intelligence (AI) and Rule-based Risk Assessment of devices based upon network exposure, known attacks, and operational criticality
- Detailed reporting of security posture, alerts, and risk
- eyeManage Features
- Unified device management and inventory across all deployments to consolidate data center, cloud, branch office, factory, IoT, and OT into one management window
- Automated distribution of IP addresses, Forescout licenses, software upgrades and backups
- Zero-touch provisioning of new appliances automates deployment expansion
- eyeRecover Features
- Failover clustering for physical and virtual appliances, even across geographically dispersed networks, through cross-cluster and even cross-site failover
- High availability pairing of active and standby appliances provide synchronized redundancy
- Forescout device backups to maintain resilience and uptime through quick recovery of failed appliances
- All modules are government certified FIPS 140-2, Common Criteria type, and more
Pros
- Vendor agnostic and will integrate with a wide range of operating systems, endpoint software, networking equipment, and third-party security tools
- Includes 20+ passive and active discovery and profiling techniques that do not require agents
- 12 Million+ device fingerprints accessible from the Forescout Device Cloud
- Active or Passive Inline Tap network connection options
Cons
- Expertise is required for troubleshooting
- One device can consume multiple licenses when using multiple IP or MAC addresses (such as connecting via wireless routers and then via ethernet cable)
- Difficult to understand required licenses to implement specific NAC features despite the availability of licensing guides
For the full list of features, pros, cons, and more details on pricing, see our in-depth Forescout Platform: NAC Product Review.

Fortinet FortiNAC
Best for IoT and OT needs
Firewall giant Fortinet offers the FortiNAC solution to provide robust network access control for a wide range of needs. Smaller organizations appreciate solutions that work for as few as 25 (virtual appliance) or 100 (physical appliance) users and larger organizations appreciate the automation for onboarding guests and Bring-Your-Own-Device (BYOD) endpoints.
In addition to basic devices, FortiNAC recognizes and supports an extensive array of non-standard endpoints such as networking equipment, internet-of-things (IoT), industrial IoT (IIoT), and operational technology (OT). These capabilities enable complex networks to consolidate and control more devices through a single NAC solution making FortiNAC a superior choice for organizations with a larger variety of possible endpoints.
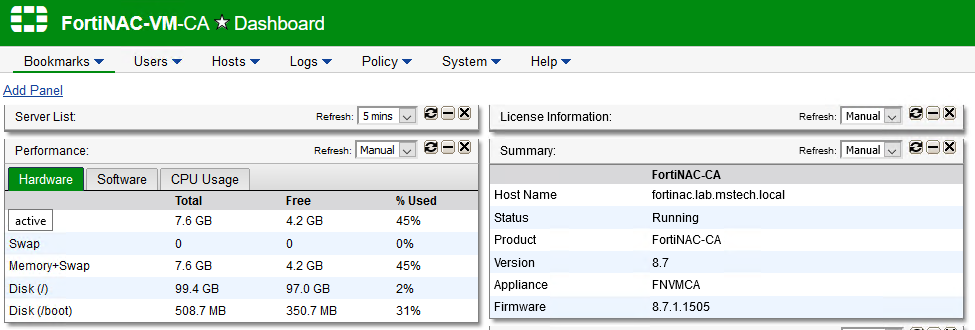
Pricing
Fortinet does not publish pricing information, but does provide an ordering guide for FortiNAC products. FortiNAC offers perpetual and subscription licenses, hardware and VM appliances, and professional services to help customers with flexible options, but also sells their products through reseller partners. This can obscure price information because partners will offer volume discounts, incentives, services, and other related products or services.
FortiNAC Hardware and Virtual Appliance Estimated Prices:
- 2,000 Network ports, suitable for SMB, FNC-CA-500C
- $21,000 or less for server with RAID, redundant power supplies
- $4,150 or less for 1 year of FortiCare Premium support
- 15,000 Network ports, mid-sized enterprise suitable, FNC-CA-600C
- $41,000 or less for server with RAID, redundant power supplies
- $8,100 or less for 1 year of FortiCare Premium support
- 25,000 Network ports, suitable for SMB, FNC-CA-700C
- $95,000 or less for server with RAID, redundant power supplies
- $19,000 or less for 1 year of FortiCare Premium support
- Optional multi-FortiNAC Management Server, FNC-CA-550C
- $41,000 or less for server with RAID, redundant power supplies
- $8,100 or less for 1 year of FortiCare Premium support
- Regular and next-gen VM servers, control and application or manager
- $3,400 or less for server
- $700 or less for 1 year of FortiCare Premium support
Once the FortiNAC server is in place, an organization needs to license the FortiNAC application itself. Fortinet offers subscription licenses that include support and perpetual licenses for which support must be purchased separately.
- Perpetual license (for the lowest tier of 100 endpoints):
- $1,100 Base software + $110 for 24×7 FortiCare Support
- $2,600 Plus software + $250 for 24×7 FortiCare Support
- $3,300 Pro software + $320 for 24×7 FortiCare Support
- Subscription (for the lowest tier of 25 endpoints):
- $200 Base software
- $355 Plus software
- $420 Pro software
Features
- Extensive non-standard device support that recognizes and controls over 2,500 network devices and millions of IoT devices
- Network discovery scans for users apps and devices, identifies rogue devices and endpoint anomalies
- Device profiling to classify types of assets and current compliance with access policies
- Firewall segmentation to isolate endpoints by policy using the firewall to create VLANs
- Customized reporting for key performance metrics, compliance reports, etc.
- Guest and BYOD onboarding (Plus or Pro Licenses) enable users to authenticate bring-your-own-device (BYOD) endpoints or guests to obtain access to the full or a limited portion of the network
- Web and Firewall Single-Sign-On (SSO) can be enabled with pro or plus licenses
- Incident response (Pro license only) features such as event correlation, audit trails, guided triage workflows, and alert criticality and routing
Pros
- Enables automation which is good for scale and ROI
- Supports IoT environments with licensed support
- Good visibility into devices on the network, including a huge array of IoT devices
- Centralizes architecture for ease of deployment and management
- Extensive third-party support through direct integrations and APIs
Cons
- Only English-language versions of scanning agents have been validated for supported operating systems
- Requires ongoing FortiCare support licenses to keep network and IoT device databases current
- Unintuitive and outdated user interface
For the full list of features, pros, cons, and more details on pricing, see our in-depth FortiNAC Network Access Control (NAC) Product Review.

InfoExpress CyberGatekeeper
Best for rapid, self-controlled NAC deployment
InfoExpress offers a family of appliances to provide NAC capabilities for a broad range of organizations. The CyberGatekeeper, CGX Access, and Easy NAC solutions deploy quickly and support enforcement for mobile, desktop, and IoT devices without any network changes required. InfoExpress NAC solutions can be the best choice for IT teams wanting to remain in control and who need simple, effective network access control that can deploy quickly.
Pricing
InfoExpress does not directly publish pricing but will offer free trials of their Easy NAC product. Appliances and software may be purchased as a perpetual license with annual support. Virtual appliances and software may also be licensed on a subscription basis.
The pricing for appliances, software, and additional modules depend upon the number of devices being managed. InfoExpress offers four physical appliances managing between 300 and 10,000 devices and two virtual appliances capable of managing between 500 and 10,000 devices. InfoExpress also offers a self-installing vLink appliance to extend appliance access to remote sites.
Features
- In-band (appliance) and Out-of-band enforcement supported through integration with existing wired or wireless network
- Network appliance agnostic
- Easy integration with many popular security and IT tools such as Bitdefender, Kaspersky Antivirus, ManageEngine Patch Manager, Microsoft Intune, SentinelOne, Sophos, Symantec Endpoint Protection Manager, Webroot, and more
- Easy and inexpensive extension to remote locations by deploying optional vLink devices that can be installed by non-IT staff
- Self-service portals for guest and BYOD users
- Automated quarantine for devices out of compliance
Pros
- Simple and quick to deploy and manage
- No network changes required for deployment
- Agentless or Agent-based scanning
Cons
- Segregated portals for Guests, Partners, and BYOD can be cumbersome and tedious to implement and support
- Unclear pricing, licensing requirements, and support options
- More basic NAC deployment than other enterprise options
For the full list of features, pros, cons, and more details on pricing, see our in-depth InfoExpress CyberGatekeeper: NAC Product Review.

Ivanti Policy Secure
Top enterprise alternative
Ivanti’s Policy Secure NAC solution can encompass local and remote endpoints to enforce foundational security policies and control network access for managed and unmanaged endpoints, including IoT. The platform integrates with a wide range of switching, Wi-Fi, and firewalls to enforce access policies and can integrate with other Ivanti products to provide zero trust network access (ZTNA) and user behavioral analytics (UEBA).
Ivanit Policy Secure can deliver enterprise-grade NAC capabilities with potentially lower total cost of ownership compared to more prominent brands, making Policy Secure a top alternative for enterprises with more constrained budgets. However, with several brand changes in ten years, many buyers may not recognize Ivanti as an established competitor in the market.
Pricing
Organizations need to obtain appliances (virtual or physical), licenses for the Policy Secure servers based upon the number of expected users, and additional licenses for optional modules. Bundled pricing, volume discounts, and pricing discounts are likely, but no pricing is officially published so organizations should contact Ivanti for quotes.
Ivanti currently sells five different hardware models and three virtual appliance configurations that service from 200 to 25,000 users without bundling. Users can download licenses from the Software Download Center using the same credentials as the Ivanti Community site. Licenses can be downloaded and managed by specific appliances or managed by a licensing server.
The appliances support four different types of licenses: Evaluation, Perpetual, Subscription, and In-Case-of-Emergency licenses. Perpetual licenses include 12 months of maintenance and support. Subscription or term licenses may be purchased for one, two, and three years and include software, updates, and support. At the expiration of a subscription, the appliance may no longer be used. Lapsed licenses require a reinstatement fee based upon the annual fee. Renewal fees typically increase by 5% per year.
Features
- Automated threat responses to indicators of compromise
- Bidirectional 3rd Party integration to improve security and auditing
- Firewalls: Checkpoint, Fortinet, Juniper, Palo Alto Networks, etc.
- Security information and event management (SIEM): IBM QRadar, Splunk, etc.
- And more: Nozomi Guardian (industrial IOT and operational technology tracking), Trellix ePolicy Orchestrator, etc.
- Built-in Behavior Analytics trained during the Policy Secure learning period
- Dynamic network segmentation based on user role and device classification
- Self-service onboarding for devices and users in known identity and access management systems
Pros
- Guest Onboarding included with the basic license instead of an add-on module
- Potentially lower total cost of ownership (TCO) for organizations with less complicated needs when compared against higher-profile competitors
- Wide operating system compatibility: Windows, macOS, Linux, Android, and iOS
- Wizard-based simple deployment, network integration, and setup ensures easy implementation and no missed steps
Cons
- Lengthy connection processes can be tedious
- Confusing licensing based upon reserved licenses, lease durations, license recall procedures, and surrendering licenses will make it difficult to predict costs in variable usage settings
- Poor brand recognition due to numerous product and brand name changes in under a decade
For the full list of features, pros, cons, and more details on pricing, see our in-depth Ivanti Policy Secure: NAC Product Review.
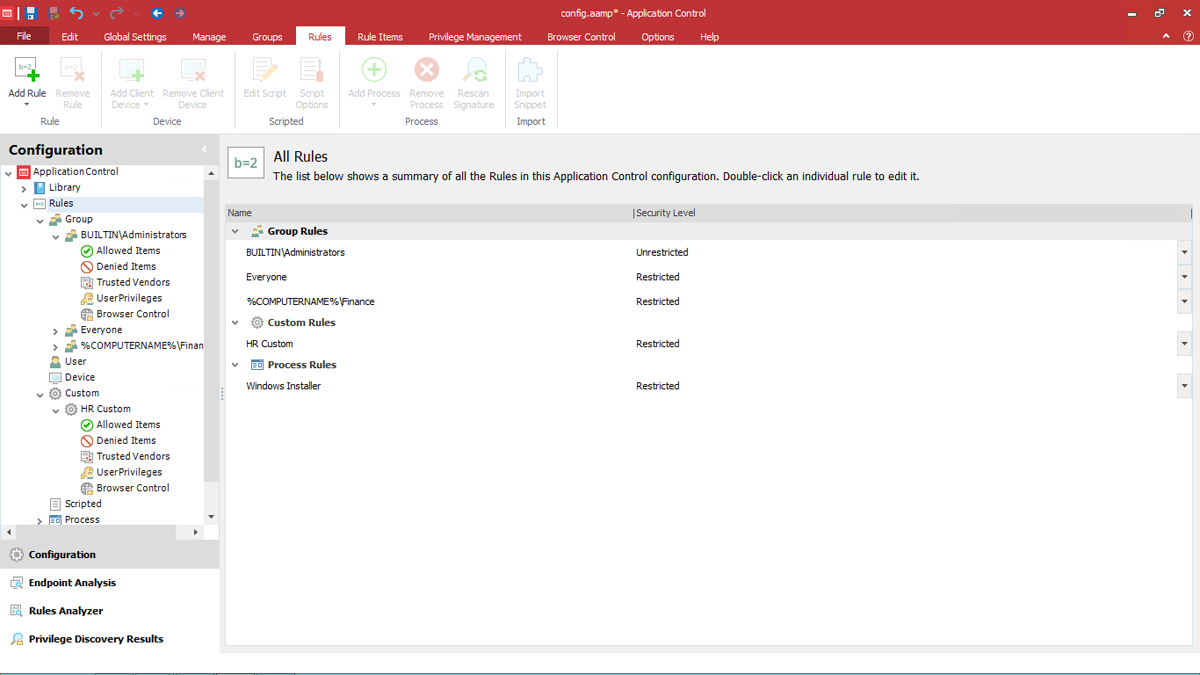
Opswat MetaAccess
Best for smaller organizations with IT expertise
Opswat MetaAccess NAC ensures every network connection and endpoint device is visible, allowed, or blocked in real time. Agentless device identification and profiling provides detailed visibility of devices, and integration with other OPSWAT technologies and third-party vendors can deliver a complete security package. OPSWAT offers a free, non-expiring license for up to 50 endpoints, which makes this solution an attractive option for smaller organizations. However, while the free tier is quite attractive, MetaAccess requires significant IT expertise to install and operate successfully.
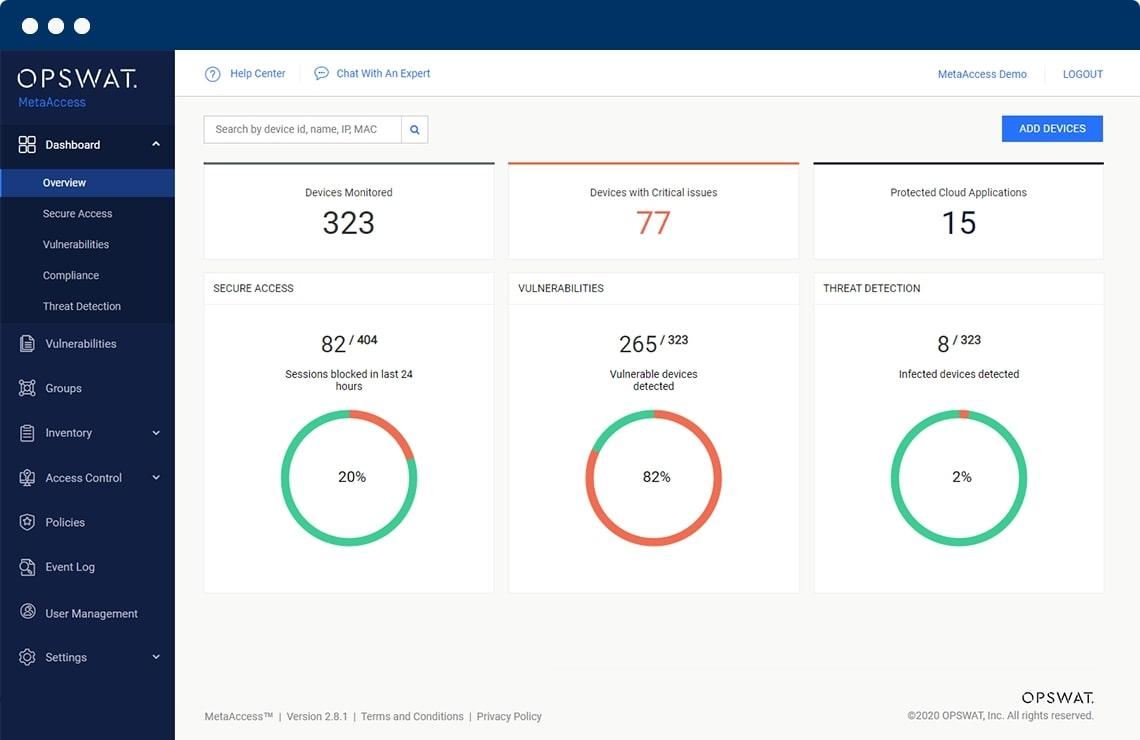
Pricing
OPSWAT does not list pricing for their MetaAccess product, but it is free to download for up to 50 licenses with no trial expiration. Once an organization determines that they want to expand their usage, OPSWAT encourages contact with their sales team or with resellers.
OPSWAT offers five different customer support plans (Silver, Gold, Platinum, Platinum In-Country for the USA, and Diamond) offering improving service level agreements, although the price per tier is also not published.
Features
- Bi-directional security tool integration with network feeds and security solutions to enable quick reactions and to enact real-time quarantines for severe alerts
- Detailed device information extracted without agents such as username, IP address, MAC address, role, device type, location, access time, and device ownership
- Real time discovery of new users and devices, including IoT
- Secure guest access, vendor access, and other third party access with granular access levels and approval processes
- Self-registration onboarding for guests and new devices through highly customizable portals
- Vendor independent deployment compatible with many network equipment vendors and a broader range of endpoints
Pros
- Integrated RADIUS server to authenticate users using the remote authentication dial-in user service (RADIUS) protocol and provide Layer 2 network control
- Optional Layer 3 policy-based routing and network control
- Simplified installation and maintenance with a five-step implementation process and remote managed services that provide proactive monitoring and nightly configuration back-ups and updated device type lists
- Works for wired and wireless networks without any need to change network design or install agents
Cons
- Unclear capacity maximums and license requirements
- Does not publish pricing to help judge total cost of ownership
- Integration and setup requires expertise, not for beginners
- Difficult to configure, challenges with server installation or 3rd party tool integration
For the full list of features, pros, cons, and more details on pricing, see our in-depth OPSWAT MetaAccess: NAC Product Review.

Portnox Cloud
Best option for small businesses
Portnox Cloud provides a cloud-native NAC-as-a-Service solution that deploys quickly and, as a SaaS solution, removes the burden of most maintenance from an organization’s IT team. Portnox offers clear pricing and a full-service installation service, which makes it the best option for small and medium-sized businesses (SMBs) to obtain NAC capabilities without heavy on-going demand for IT expertise. Portnox Cloud offers a low total cost of ownership for smaller organizations, but larger enterprises may have the expertise to obtain more benefits and control with an in-house NAC solution.
Pricing
Portnox offers a thirty-day free trial and some of the most transparent pricing in the NAC market:
- Portnox RADIUS+ Network Authentication: Up to $2 per device per month ($1,000 per month minimum)
- Portnox TACACS+ Network Device Administration: $200 per admin per month, 1 admin and 100 device free account available without expiration
- Portnox ZTNA: Up to $5 per device per month ($1,000 per month minimum)
Several add-on packages are also available such as “white-glove” managed onboarding service available for $3,500 and extended guest account packages. Discounts are also available based upon volume and for education or non-profit customers.
Features
- Portnox RADIUS+ Network Authentication
- Implements in under 30 minutes with no installations required
- Tried-and-true technology using the Remote Authentication Dial-In User Service protocol and built-in RADIUS proxy and RADIUS Forwarding
- Does not require passwords when using device MAC address characteristics (AKA: MAC Authentication Bypass) as an authentication factor
- Selectable access layers
- Integrates with Directory service (Active Directory, LDAP)
- Easy-to-Define security groups and role-based authentication
- Anti-Flood protection against DDoS attacks
- Location-based access policies
- Portnox TACACS+ Network Device Administration
- Centralizes Authentication for multiple user databases such as Open LADAP, Active Directory (AD), Azure AD, Google Workspace, Okta, and more
- Enable granular authorization with varying levels of privilege, services allowed, commands, and more
- Consolidated network accounting to track user activity (identities, start/stop times, executed commands, etc.) across all network devices to streamline audits and reporting
- Integrates via RESTful API with security information and event management (SIEM) solutions
- Customizable risk policy based on the mode of access (wired, VPN), location, requested network device, etc
- Portnox ZTNA
- Vendor agnostic zero trust network access control
- Detects and quarantines non-compliant devices based on firewalls, antivirus, applications, USB drives and more
- Enables device remediation for non-compliant devices
- Guest self-onboarding and up to 50 daily guest accounts; SMS-based and Sponsor-based onboarding also supported
- Device assessment using Portnox AgentP and agentless assessment
- Automated discovery of all devices
- Monitoring of traffic and monitoring-only mode
- Multi-region RADIUS redundancy
Pros
- Fully cloud-native
- No hardware to maintain, update, and manage
- Maintenance free and no need for backups or special security
- Covers wired, Wi-Fi, and VPN network access
- Real time visibility of access attempts into the network
- Centralized administration, control, authentication, and reporting
- Applies to all devices from managed laptops to BYOD mobile phones or even security cameras (IoT) or heat sensors (OT)
- Network hardware agnostic and does not require network redesign
- Solid basic NAC
- Low entry price when considering the reduced total cost of ownership from reduced labor to maintain, update, and administer the NAC solution
Cons
- Screen lags can occur
- Port status inconsistencies cited by customers between switch and Portnox port status
- Lacks features compared to other competitors
- Maintains a smaller database of IoT devices, but offers an add-on AI-powered IoT fingerprinting solution
- May be more expensive than self-administered options for larger enterprises
- SaaS removes direct control from the organization
What is Network Access Control (NAC)?
Network access control (NAC) plays two critical roles for an organization, improving security and saving costs. To improve security, NACs no longer assume that any device that can connect to a network is safe and therefore examine each device as they establish a connection. This process provides upgraded security when compared with more passive VPNs and intrusion detection and prevention systems (IDS/IPS/IDPS). NACs set policies for access based on resource, role, device, and location-based access as well as enforce security compliance requirements and patch management policies.
To reduce costs, NAC solutions automate significant IT and Help Desk tasks such as on-boarding for new corporate devices, BYOD and guest accounts based upon pre-established rules. NACs both strengthen security as well as save costs by denying access or quarantining non-compliant devices until users navigate automated remediation processes.
The Increasing Importance of NAC
In a modern network, the number of devices trying to connect to networks continues to increase in both variety as well as in the method of connection.
Connections continue to be required by in-house personnel, networking equipment, local data center servers, and corporate peripherals such as printers, and storage array networks (SANs). Meanwhile, remote employees, customers, consultants, contractors, and guests also want to connect to resources using a mix of corporate controlled and BYOD laptops, tablets, and mobile phones. Each group requires distinct and varying levels of access to network resources and applications.
Meanwhile, a host of non-user devices also seek to make network connections from devices categorized within the internet of things (IoT), Operations Technology (OT), Industrial Control Systems (ICS), industrial IoT (IIoT), and medical technologies. These devices often lack operating systems that would support antivirus or other endpoint security solutions and therefore need extra protection and isolation to protect against potential attacks.
Lastly, the expansion of Wi-Fi and wireless access points now includes semi-public venues such as sports stadiums, concert venues, airports, restaurants, and churches. These venues often seek to allow limited, but controlled network access to their guests and NAC solutions can enable high-volume on-boarding in a safe and controlled manner.
16 Considerations When Choosing a NAC
Network Access Control solutions can offer many different capabilities and levels of security and access. Ultimately, each organization needs to define their needs and then match the capabilities of the NAC against those needs based upon the following capabilities and considerations.
- Access control: can the tool grant access at the level of granularity needed to satisfy the organization’s security, risk, and compliance requirements to block, quarantine, and grant varying degrees of access.
- Agents or Agentless functions provide important tradeoffs to consider. The most robust solutions offer both options, but each organization needs to consider their use cases. Agents can bog down user experience and impact individual machine performance, but organizations desiring deeper insights into endpoints may consider the trade-off to be valuable. Agentless solutions can provide detection and insights for new devices when they first log into the network, but often cannot exercise direct control over the devices themselves.
- Automated guest access management and automation should be able to handle the organization’s expected volume and type of guest access.
- Automated onboarding of corporate and BYOD devices should be considered to remove the burden of set-up and approvals from the IT or Help Desk teams.
- Asset discovery, visibility, and profiling of new devices is important to monitor, secure, and provide appropriate access to every new endpoint (workstations, laptops, IoT, etc.). Tool should at least be able to discover and manage the majority of the expected endpoint types and volume of users for the network and should automatically block rogue devices.
- Base license capabilities can be difficult to determine without careful investigation, but will be important to determine costs. Vendors will often advertise a large number of features without explicitly noting that many features may only be available with the addition of additional licenses and appliances.
- Centralized management enables consistent delivery of policies and protection across the network and multiple NAC devices without increasing labor costs.
- Compatibility with existing networking equipment and security tools will be critical to determining the difficulty in implementing a NAC solution and its ability to function as intended.
- Network segmentation options will be supported by some tools to limit east-west navigation by attackers.
- Policy management should provide sufficient capabilities to define and administer security configuration requirements, assign access levels to specific groups, and specify the specific actions for the NAC to take with both compliant and non-compliant endpoints.
- Regulatory compliance continues to increase in importance for many organizations as more data becomes regulated. Most NAC solutions will fulfill the broad compliance requirements for various standards, but organizations will need to ensure that the specific tool selected can produce the needed reports to document that the organization is in compliance.
- Security integration with third-party security applications such as security information and event management (SIEM) systems and next-generation firewalls (NGFW) can accelerate security responses, enable more robust responses to threats, and increase the context and utility of alerts. Some NAC tools will even have built-in security functions to provide additional protection.
- Security posture evaluations examine endpoints attempting to connect to the network and should determine the suitable level of access based upon the organization’s rules for security controls (antivirus presence, software updates, etc.).
- Sufficient support will be required to enable even the best NAC tools to perform as intended. Organizations need to honestly evaluate their capabilities and consider what levels of support will be required for installation, configuration, tuning, maintenance, monitoring, and ongoing management of the NAC solution. Organizations that need more support than offered by the baseline support level of their preferred tool may need to consider a more turn-key solution, premium support, or outsourcing to a managed service provider (MSP) or managed security service provider (MSSP).
- Total cost of ownership of the solution will depend upon the appliances (physical or virtual), software licenses, add-ons needed to achieve required features, and support contracts. Organizations need to understand what may be required to meet the minimum, expected, and preferred capabilities for the solution, as well as the labor required to install, configure, maintain, and manage the solution.
- Unused features may be expensive options. Some products may offer more features or more expansive databases of supported products, but those extras also usually come attached to higher total costs of ownership. If the organization doesn’t use those features or products, then they are paying a premium for no additional utility.
How the Top NAC Solutions Were Selected
In creating this list, our team reviewed a large number of sources, including user reviews, product capabilities, and market expectations. We evaluated the capabilities of the tools in the context of the fundamental network access control requirements as well as the likely needs of various customers.
At the time of publication, the nine tools above provided compelling options for organizations seeking NAC capabilities. Other NAC options that organizations might want to consider include:
- AWS Resource Access Manager: NAC for Amazon Web Services
- Google Cloud Identity-Aware Proxy: NAC for Google Cloud resources
- openNAC: Open source NAC solution
- PacketFence: Open source NAC solution
- ThreatLocker Network Access Control: this solution uses firewall technology installed on endpoints to protect devices and exert network access control
Other types of network security technologies can provide similar device control functions as NAC, such as secure web gateways, secure-access service edge (SASE) solutions, some next generation firewalls (NGFWs), unified secure access (endpoint security plus network control), and zero trust network access (ZTNA) solutions. IT teams could even manually create MAC address whitelists of approved devices to implement rigid network access control with no tool costs.
Although each alternative solution may have merit, we assume that organizations seeking network access control specifically needed a tool to provide core NAC functionality and we thus excluded tools such as:
- Barracuda CloudGen Firewall: An NGFW with some NAC features
- Citrix Gateway: a software defined wide area network (SD-WAN) solution with SASE and NAC features
- Infraray BICS: Once a popular European NAC solution named Auconet BICS, now an IT infrastructure management tool with NAC features
- Secure Gateway solutions or cloud VPN services with NAC features (NordVPN, Perimeter 81, and others)
- McAfee Unified Secure Access
- NordLayer: ZTNA and SASE solution with NAC capabilities
- SAP Access Control: an identity governance and management tool with NAC features
- SonicWall Secure Mobile Access: unified secure access gateway
- Sophos ZTNA
- Twingate ZTNA
As the market continues to evolve and shift, this list will continue to be updated and changed to reflect added capabilities from the various vendors.
Bottom Line: Control Network Access ASAP
Every organization needs to control network access as network connections continue to grow in number and variety. Each connection increases the risk of breach and attackers are lined up to exploit every weakness they can find. Fortunately, the variety of NACs and technology with NAC features provide a range of effective choices for the entire spectrum of needs and resources. Some organizations may be compelled by regulatory or other external forces to pursue NAC, but every organization can benefit from the risk reduction and cost savings provided by the effective control of users and devices.
Further reading:
- Best Identity and Access Management (IAM) Solutions
- Best Third-Party Risk Management (TPRM) Tools
- Best Privileged Access Management (PAM) Software
- Best Zero Trust Security Solutions
eSecurity Planet Editor Paul Shread contributed to this report written by Drew Robb on January 24, 2022 and revised by Chad Kime on April 15, 2023.


